Autonomous Cyber Risk Validation
Piscium is a Continuous Threat Exposure Management platform that automates the assessment of cyber security risks by identifying vulnerabilities and prioritizing them based on their impact on business goals.
0
Operational layers — Discovery, Analysis, Action
0+
Compliance frameworks mapped
0+
Native connectors in marketplace
0/7
Autonomous agent validation
Core Capabilities
Comprehensive security automation for continuous threat exposure management.
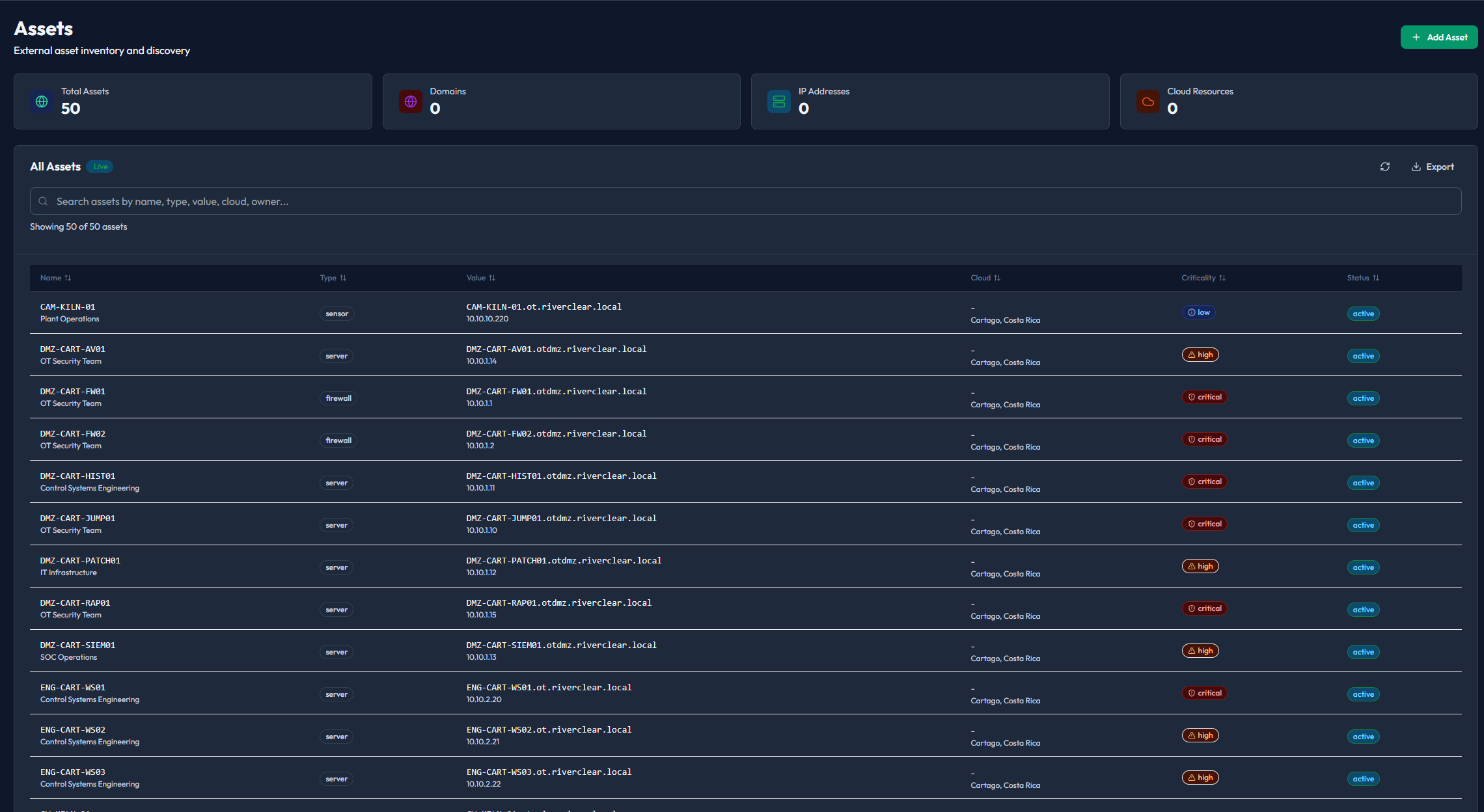
Precision Asset Inventory
Piscium's discovery engine provides granular visibility across IT, OT, and Cloud domains.
- Real-time Criticality Scoring
- Multi-Cloud & Hybrid Support
- Automatic Asset Fingerprinting
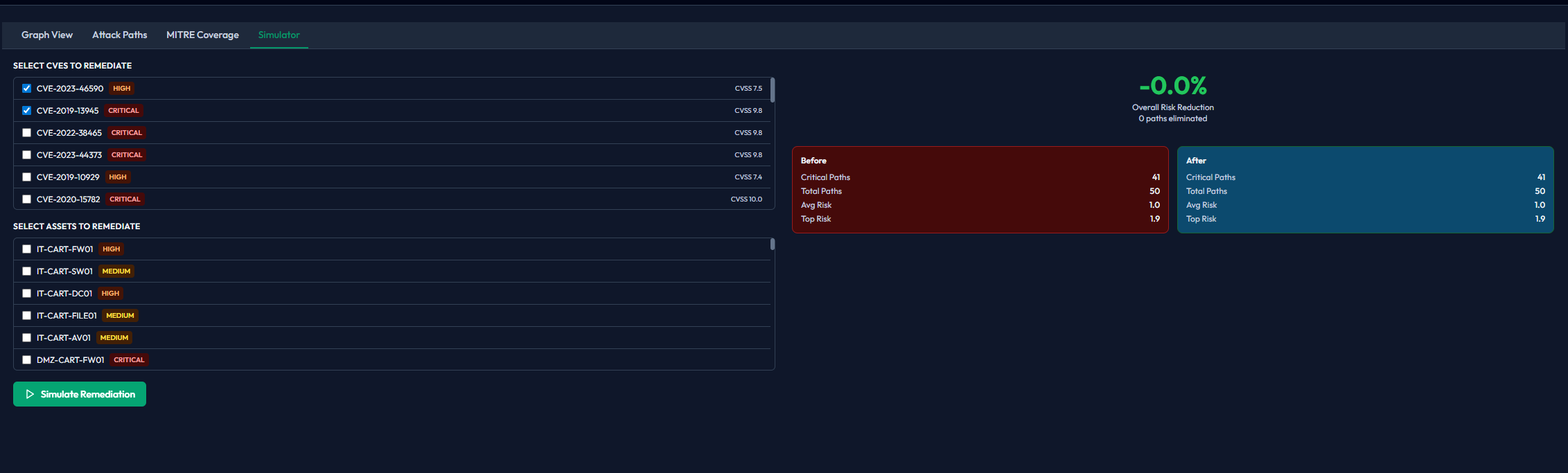
Dynamic Attack Graphs
Visualize lateral movement paths through your hybrid infrastructure with mission-critical clarity.
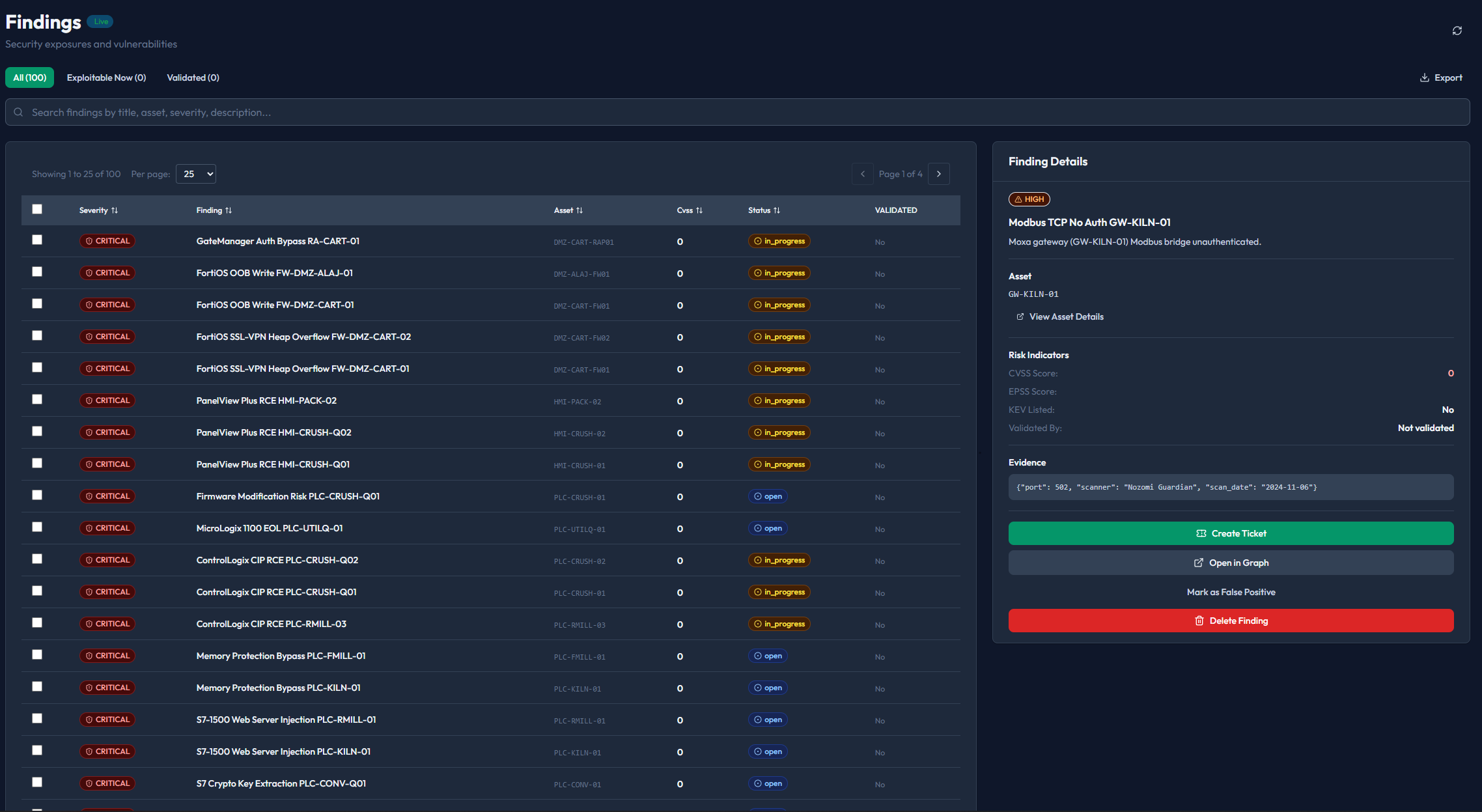
Actionable Findings
Prioritize risks based on business impact and architectural validation status.
Remediation Orchestration
Bridge the gap between security and IT with automated ticket generation and step-by-step remediation playbooks.
The Continuous Cycle Architecture
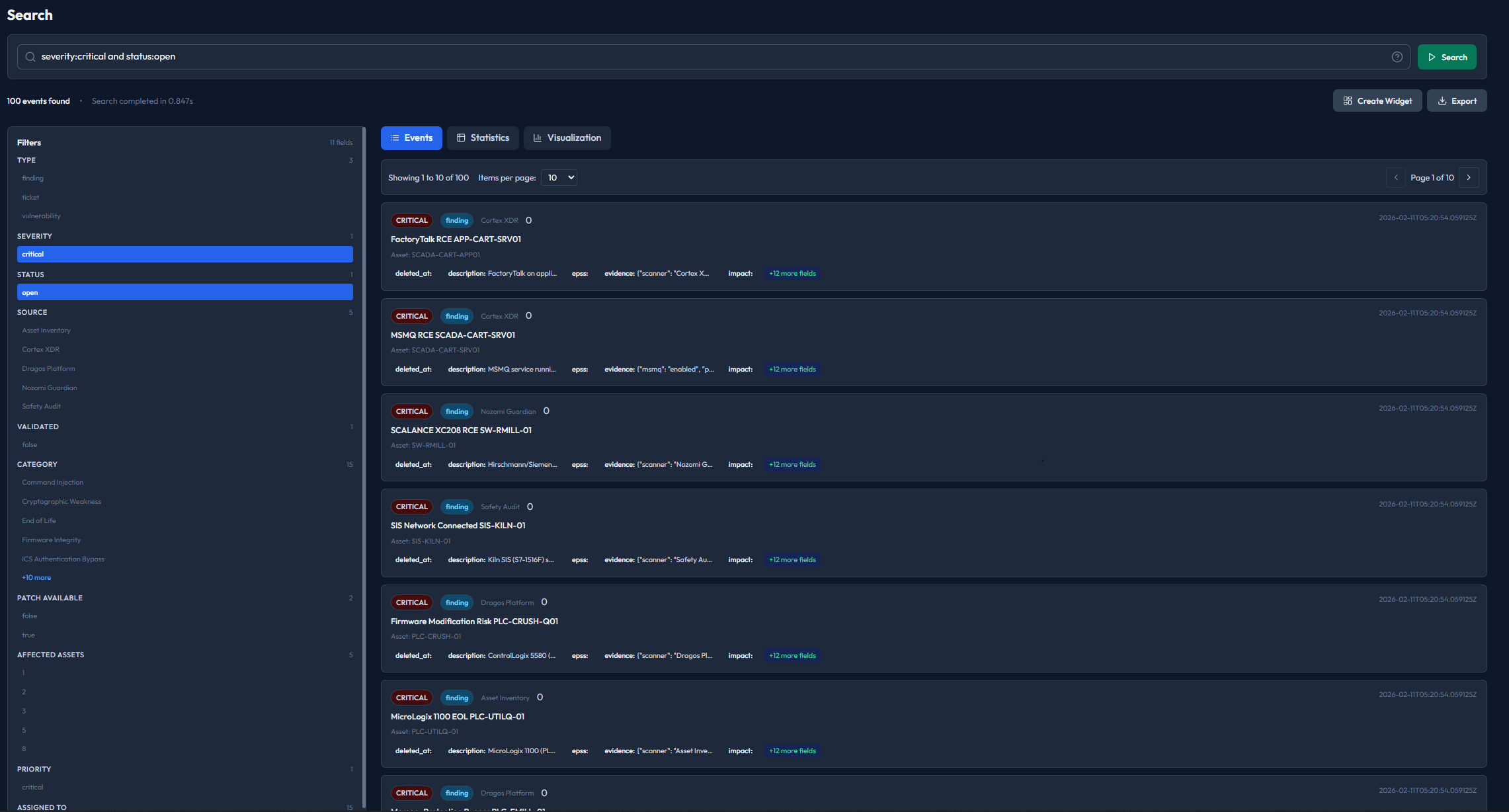
Connectors ingest data from your entire attack surface. The CTEM engine discovers, prioritizes, and validates exposures, then pushes remediation to your existing tools.
Discovery
Automated identification of all assets, known and unknown, across IT, Cloud, and OT environments.
Analysis
Real-time simulation of attack vectors to validate which vulnerabilities are actually exploitable.
Action
Precision remediation instructions and automated integration with existing ticketing systems.
Built for OT/ICS
Unlike traditional IT scanners, Piscium is engineered for the unique constraints of operational technology and industrial control systems.

Frequently Asked Questions
How does Piscium differ from traditional vulnerability scanners?
Is Piscium safe to use in production environments?
Does Piscium support hybrid and multi-cloud environments?
What compliance frameworks are supported out of the box?
Ready to See Piscium in Action?
Discover why leading critical infrastructure organizations trust Piscium for continuous risk validation and exposure management.